Before security teams deploy controls, they need clarity on the objective. This topic centers on the three foundational commitments of information security: keeping data restricted to the right people, keeping it accurate and trustworthy, and keeping it available when the business needs it.
The CIA Triad: Security’s Core Commitments
The CIA Triad is not a memorization item to park for the exam. It is the baseline lens used to evaluate systems, incidents, and controls. When a breach or failure happens, the first diagnostic question is usually which part of CIA was primarily impacted.
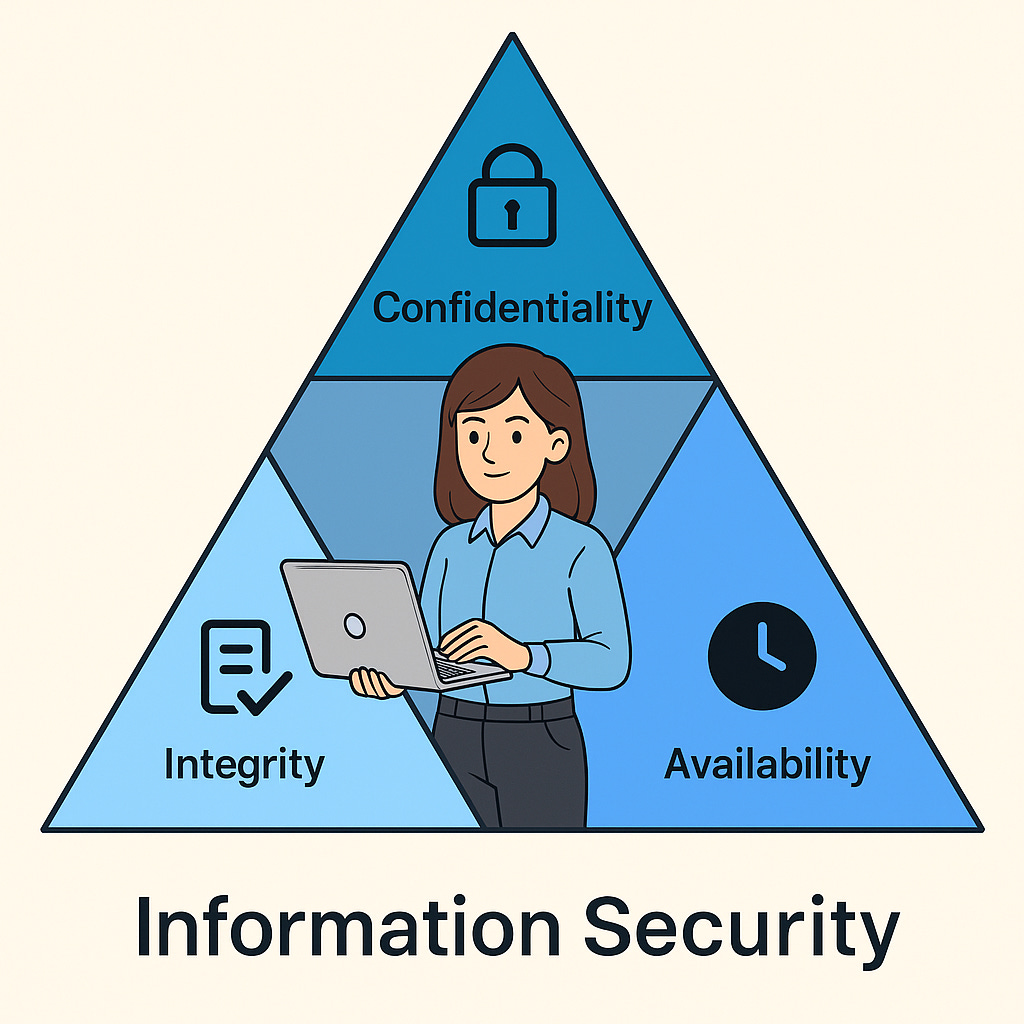
Confidentiality → Preventing Disclosure
Confidentiality is about restricting access and exposure. The goal is simple: information should be visible only to authorized subjects. In practice, that includes both technical and administrative measures.
- Access controls, both physical and logical
- Encryption at rest and in transit
- Least privilege
- Need-to-know restrictions for sensitive data sets
Typical confidentiality failures: exposed cloud storage, phishing-driven disclosure, lost unencrypted laptops, and internal snooping beyond role boundaries.
Integrity → Preventing Unauthorized Alteration
Integrity is the assurance that data stays accurate, consistent, and trustworthy. If payroll values, logs, or financial records are altered without authorization, confidentiality may still be intact, but integrity is broken.
- Hashing to detect tampering
- Digital signatures to validate source and integrity
- Formal change control
- Separation of duties
- Tamper-resistant or immutable logging
Typical integrity failures: manipulated transactions, altered audit trails, malicious firmware, or silent errors from bad ETL or formula changes.
Availability → Preventing Destruction or Downtime
Availability means the service, system, or data remains reachable and usable when required. Security is not complete if the business cannot operate. This is why resilience, redundancy, backups, and continuity planning sit directly inside the security conversation.
- Backups and restore capability
- RAID and redundancy patterns
- High-availability architectures
- DDoS protection and rate limiting
- Business continuity and disaster recovery planning
Typical availability failures: ransomware, single points of failure, data center outages, destructive misconfiguration, and lack of tested recovery paths.
Authenticity and Non-Repudiation
CIA explains what must be protected. Authenticity and non-repudiation sharpen accountability. Authenticity answers whether the subject or system is really who it claims to be. Non-repudiation answers whether that actor can later deny the action.
- Authenticity: validating identity through mechanisms such as smartcards, certificates, or strong authentication.
- Non-repudiation: creating evidence through digital signatures and secure logs so actions remain attributable.
What Security Governance Actually Does
Governance is the structure that turns security from isolated tooling into directed business behavior. It defines who decides, who owns risk, who approves direction, and how security aligns with mission and strategy rather than operating as a side function.
In this framing, governance exists to keep risk at an acceptable level while ensuring that security supports business goals. That means policies, roles, reporting lines, decision rights, and control direction are not administrative filler. They are the mechanism that keeps security coherent.
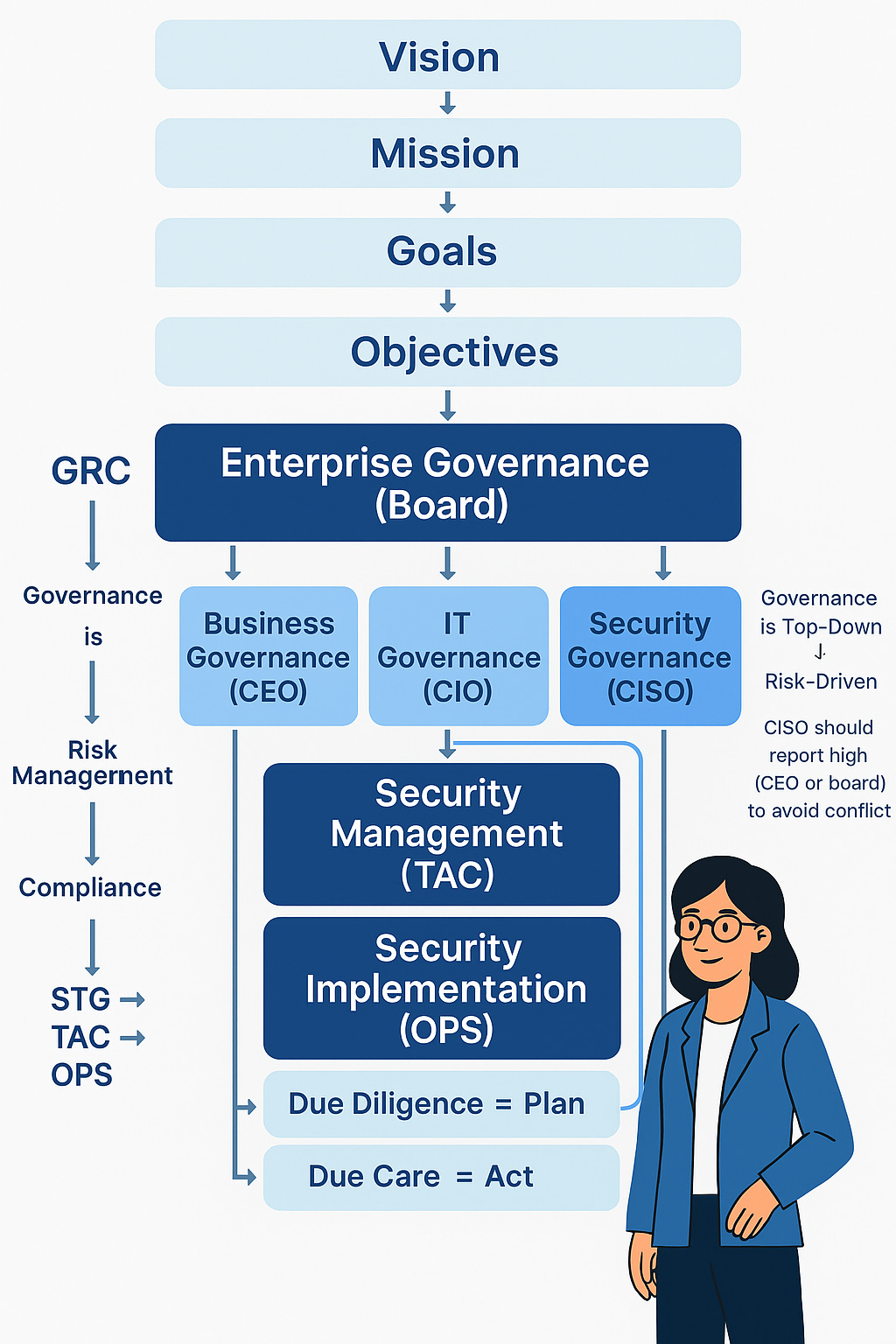
Governance Layers in Practice
- Vision and mission: define what the organization exists to do
- Goals and objectives: break that direction into measurable priorities
- Strategy: sets the high-level path
- Tactical management: turns strategy into departmental plans
- Operations: executes daily control activity
Core Governance Components
- Risk assessment and prioritization
- Defined roles and responsibilities
- An information security program with policies and procedures
- Security management that translates policy into plans
- Security operations that implement, monitor, detect, recover, audit, and improve
Due Diligence vs Due Care
This distinction matters because CISSP questions often separate assessment from action. Due diligence is the discovery and evaluation phase. Due care is the implementation phase once the organization knows what the risks are and what treatment is required.
Due diligence: investigate, assess, analyze.
Due care: implement, enforce, operate.
A practical example is vendor security review. Assessing the cloud provider’s controls is due diligence. Enabling MFA, adjusting policy, and rolling out staff training based on that assessment is due care.
Brain Ticklers
Q1. A payroll team cannot access critical data before disbursement because of a single misconfigured server acting as a point of failure. Which CIA element is primarily impacted?
Think: this is a service access problem, not a disclosure or tampering problem.
Q2. A CISO performs a vendor risk assessment, and the team later enables MFA, deploys endpoint agents, and trains staff. Which action is due diligence, and which is due care?
Think: assess first, act second.
Q3. An IAM specialist drafts access control policies after zero-trust direction is approved by leadership. Which governance tier best describes that work?
Think: this is translating approved direction into implementable plans.
Q4. A CISO wants to report higher than the CIO to reduce conflicts where security priorities lose to IT delivery or budget concerns. Why?
Think: independence and conflict-of-interest reduction.
Q5. An attacker exploits SQL injection to alter invoice values and insert fake transactions. Which CIA element is compromised?
Think: unauthorized modification.